 We use phishing techniques to attempt to infect user computers or trick users to divulge sensitive information. Email Phishing will measure how many users fall for the phishing ploy and click on a link or open an attachment.
We use phishing techniques to attempt to infect user computers or trick users to divulge sensitive information. Email Phishing will measure how many users fall for the phishing ploy and click on a link or open an attachment.
We emulate cyber criminals with our email phishing services by using the same techniques they use. Unlike automated phishing services that use canned templates, we perform research on your organization and users. We use many tools and Open Source Intelligence (OSINT) methods to gather useful information to use for phishing, spearphishing, and whaling techniques against your users. We use a combination of manual methods and automated tools to provide realistic phishing campaigns, targeted for your unique environment and users.
If you already utilize an automated phishing training service that takes users that fall for the phishing templates to a phishing training website or CBT, our phishing service is perfect to validate the effectiveness of your phishing training service. Training without validation is useless.
If you do not use an existing phishing training service or do not have an existing cybersecurity awareness program, we recommend testing your users with our phishing service, then following up with our cybersecurity awareness training. We’ve found this approach very effective, because we use the results from the phishing campaigns in the cybersecurity awareness training to make the training relevant and tangible. Many users do not understand the dangers of phishing and what type of actions an attacker can take on their system if they simply visit a website (link within the phishing email) or open an attachment. We show the attacker perspective of the phishing campaign to make the threat real and relevant.

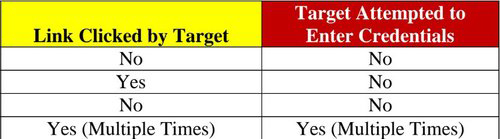 The Phishing Report covers tactics used for the email phishing campaigns, as well as any other authorized social engineering tactics. Phishing analytics will be provided for an email campaign that show how many users “fell” for the tactic used by clicking on a link or opening an attachment. Samples of phishing emails are included in this section of the report.
The Phishing Report covers tactics used for the email phishing campaigns, as well as any other authorized social engineering tactics. Phishing analytics will be provided for an email campaign that show how many users “fell” for the tactic used by clicking on a link or opening an attachment. Samples of phishing emails are included in this section of the report.