If you are anything like myself and my co-workers at Alpine Security, you’re obsessed with Cybersecurity and the impact of poor implementations. If you’re not like us, good for you! But there are still some things you ought to be aware of to help you protect your data, especially when traveling.
I am an avid and enthusiastic amateur photographer, and I often plan trips specifically to indulge this hobby. This means I travel with an array of electronic devices that includes my camera body, multiple lenses, external storage to backup photos, as well as my iPhone (unlocked) and perhaps my iPad, or a dedicated eReader. For those long flights to exotic places I’m partial to my old, but venerable Sony PRS 950 7” eReader. Everything is password protected and encrypted.
So Many Gadgets
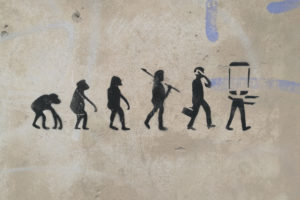
Traveling for business is different, of course. Today, we all travel with a plethora of electronic gadgets that generally include laptops, smartphones, tablets and all the associated bits and bobs and plugins. And all those devices have personal and sensitive business data on them, which we might not necessarily want a border agent to see. So how do we keep that data confidential?
There are a variety of ways to accomplish this. Let’s look at keeping business data secure first.
The absolutely simplest way to keep data safe while traveling is to not travel with any electronic gadgets. Of course, that isn’t possible in today’s always-connected business environments. There is also shipping. This method requires us to box up our electronic gadgets and ship them to our destination using a secure service such as FedEx or UPS. And, again, this isn’t really a viable option if we are shipping across borders because we’ll still have to deal with customs. So what do we do? In the Security+, CISSP, CyberSec First Responder and various other cybersecurity courses the standard recommendations are to always protect devices with strong passwords/passphrases. And, of course, this is a good idea always, but what happens if we get stopped at a border and ordered to unlock a laptop or smartphone or tablet for inspection?
Crossing the Border
We can always refuse. Doing that, though, can also cause us trouble as there is the possibility we might be detained until we agree to the search. In early 2017 a scientist for NASA’s Jet Propulsion Lab, a U.S. citizen, was returning from a trip to Chile when he was detained at the border until he unlocked his smartphone. This device was owned by NASA and as you can imagine JPL’s cybersecurity team probably wasn’t pleased about the breach. And it was a breach, since an unauthorized person had gained access to the data contained on the smartphone, and possibly copied it. I’m sure there aren’t many of us who would want to be indefinitely held up returning from an overseas trip and after a long flight. What can we do, though?
The best solution is to travel with gadgets that don’t store any sensitive data on them to begin with. Or use gadgets that can be quickly wiped and restored later. A standard laptop can be a bit problematic, but if we have data that needs to be accessed and removed quickly we can use a cloud storage solution such as Dropbox, Google Drive, or Apple iCloud. In the case of the former two, to remove any sensitive data just turn off the service and uninstall the apps (if you are using the service that way) and in the latter case disabling an iCloud account will offer the option to remove all the data from the device. Later, at the hotel, you can then download the data you need or reinstall the particular service’s app if you prefer. These services work much the same way for iOS and Android-powered devices. If you don’t necessarily need a full-featured computer laptop, perhaps you might want to go with something like a Chromebook. These devices don’t store anything on them, by default, and make very good travel devices.
If you don’t mind a bit of inconvenience and need a process that is a little more thorough for a smartphone or tablet you’ll need a recent backup in the cloud then you can restore the device to a factory state when crossing the border then restore the backup when you reach your destination. Also, when crossing borders, be sure to disable fingerprint and face recognition features. The simplest way to do this is to restart the smartphone before getting off the airplane.
Summary
The long and short of this advice to make sure sensitive data does not fall into unauthorized hands while traveling is to not have that data on you. Strong encryption and VPNs should also be used to protect data. How you protect your data is ultimately up to you, and there are additional methods beyond what I’ve talked about in this article, but hopefully you will be able to use this information to your advantage and keep unauthorized people from accessing your data.
Author Bio
 Michael with his foster pit bull, Toby
Michael with his foster pit bull, Toby
Michael Allbritton is a Cybersecurity Analyst and Trainer with Alpine Security. He holds several security-related certifications, including Certified Information Systems Security Professional (CISSP), Network+, Security+ and CyberSec First Responder (CFR). Michael has many years of experience in software testing, professional services, and project management. He is equally comfortable working with software engineers on testing and design and with sales to meet and manage customer expectations. Michael’s cybersecurity experience with Alpine includes penetration testing, vulnerability assessments, and social engineering engagements for various clients as well as teaching courses for the above-mentioned certifications.
In his spare time Michael is an enthusiastic amateur photographer, diver, and world traveler. He has photographed wildlife and landscapes in the United States, Africa, Central America, West, and East Europe and has amassed several hundred dives as a PADI Divemaster.